How IT Asset Disposition Protects Your Company’s Data Security
From customer records and financial data to intellectual property and internal communications, company data is one of the most valuable assets any organization possesses. While businesses invest heavily in cybersecurity systems, many overlook an important stage in the lifecycle of their technology infrastructure: what happens to IT equipment after it is no longer in use.
Old laptops, servers, storage devices, and desktops often contain confidential data even after they are replaced or retired. If these devices are not handled properly, they can become a serious risk to organizational data security. This is where the process of IT asset disposition becomes essential.
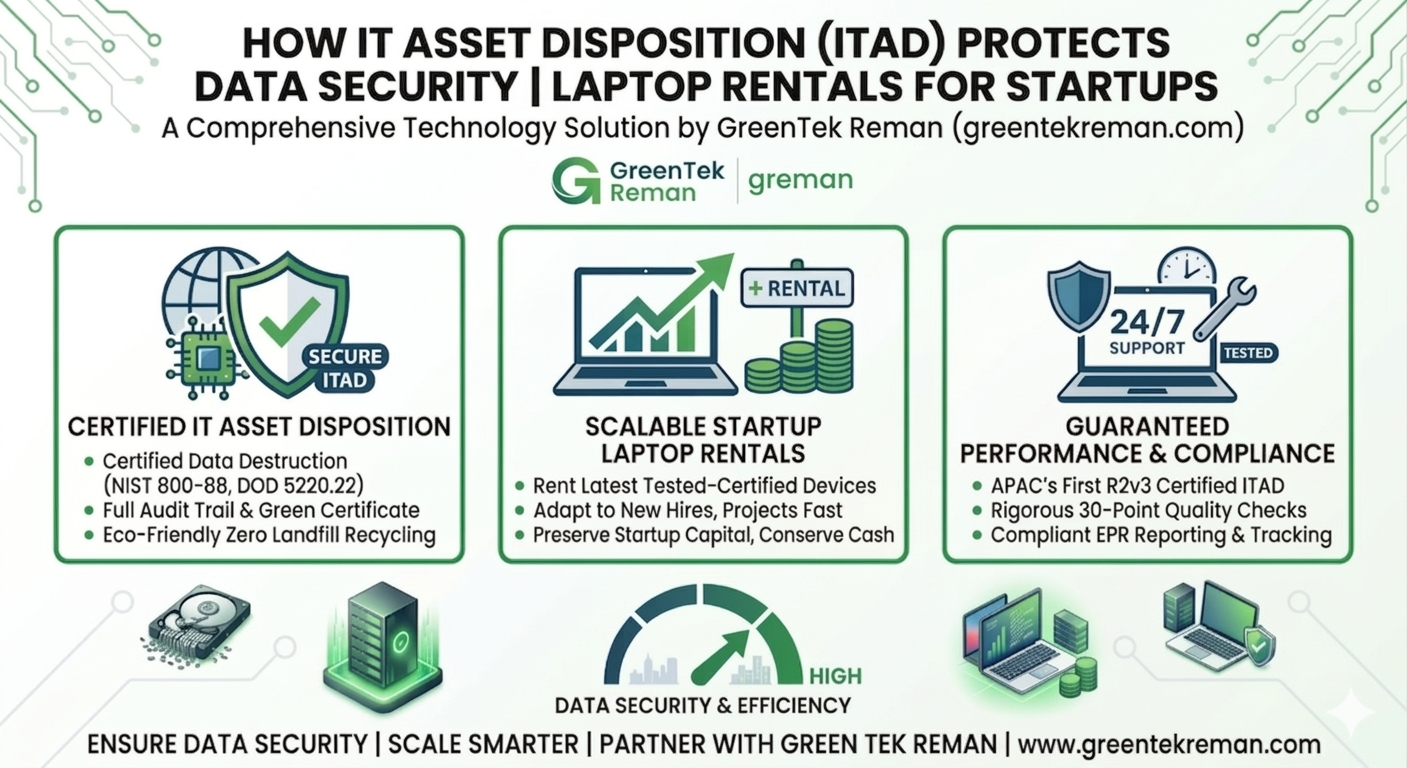
IT asset disposition, commonly referred to as ITAD, involves the secure, responsible, and compliant handling of obsolete or unwanted IT equipment. It ensures that devices are properly sanitized, recycled, or repurposed without exposing sensitive information. In addition to protecting business data, IT asset disposal also helps organizations comply with environmental regulations and corporate sustainability goals.
Understanding the Risks of Improper IT Asset Disposal
Many organizations focus on protecting their data while systems are actively in use. Firewalls, encryption, access control policies, and monitoring tools are widely implemented to safeguard information. However, once hardware devices reach the end of their lifecycle, they may be stored, resold, donated, or discarded without adequate security precautions.
Improper IT asset disposal can lead to serious data breaches. Hard drives, solid-state drives, and storage media often retain recoverable data even after files are deleted or systems are formatted. If these devices fall into the wrong hands, sensitive information can be extracted using specialized data recovery tools.
Data breaches caused by discarded hardware can have significant consequences. Companies may face financial losses, legal liabilities, regulatory penalties, and damage to their brand reputation. Customers and partners expect organizations to protect their information at every stage of the technology lifecycle.
By implementing structured ITAD practices, businesses can eliminate these risks and ensure that retired equipment does not become a gateway for data leaks.
What Is IT Asset Disposition and Why It Matters
IT asset disposition refers to the systematic process of managing obsolete or surplus IT equipment in a secure and environmentally responsible manner. The process involves several steps designed to protect data security while maximizing the value of retired hardware.
Typically, IT asset disposition includes asset tracking, secure data erasure, device testing, refurbishment when possible, and environmentally compliant recycling for devices that can no longer be reused. Each step ensures that organizations maintain control over their data even when hardware reaches the end of its operational lifecycle.
For businesses that regularly upgrade their technology infrastructure, ITAD services provide a reliable method for handling old equipment without creating security vulnerabilities. By working with professional ITAD providers, organizations can ensure that sensitive information is permanently removed before devices are reused or recycled.
The Connection Between ITAD and Data Security
Secure data destruction is the most critical component of IT asset disposition. Many storage devices contain fragments of information even after standard deletion processes. Without proper sanitization, these remnants can still be recovered.
Professional ITAD services use specialized techniques to eliminate data completely. These techniques may include software-based data erasure, degaussing, or physical destruction of storage media depending on the sensitivity of the information stored.
Software-based data wiping overwrites the entire storage device multiple times with random patterns, making data recovery virtually impossible. Degaussing neutralizes magnetic fields in storage media, permanently destroying the data stored on the device. In cases where maximum security is required, physical shredding of storage drives ensures that the data cannot be reconstructed.
By implementing these processes, organizations can protect their data security even when hardware devices leave their premises.
Regulatory Compliance and Data Protection Requirements
Many industries are governed by strict data protection regulations that require organizations to manage sensitive information responsibly. Financial institutions, healthcare providers, government agencies, and technology companies must follow compliance frameworks that dictate how data should be stored, handled, and destroyed.
Improper IT asset disposal can lead to violations of these regulations if sensitive information is exposed through retired hardware. Organizations may face heavy penalties if regulators determine that they failed to protect customer or employee data.
ITAD processes help businesses maintain compliance by providing documented proof that data destruction procedures were followed correctly. Reputable service providers typically offer certificates of data destruction and detailed asset tracking reports.
These records demonstrate that organizations have taken the necessary steps to safeguard sensitive information and comply with regulatory requirements.
Protecting Corporate Reputation Through Secure Asset Management
In the modern digital economy, trust plays a major role in business success. Customers expect companies to handle their personal and financial information responsibly. A single data breach caused by improperly discarded IT equipment can damage years of trust built with customers and partners.
Media coverage of data breaches often highlights how sensitive information was recovered from old computers, servers, or storage devices that were discarded without proper data sanitization. Such incidents can severely impact an organization’s reputation and customer relationships.
Implementing a structured IT asset disposition strategy demonstrates that a company takes its data security responsibilities seriously. It reassures stakeholders that sensitive information is protected throughout the entire lifecycle of the technology infrastructure.
Environmental Responsibility and Sustainable IT Disposal
In addition to protecting data security, IT asset disposal plays a crucial role in environmental sustainability. Electronic devices contain materials such as metals, plastics, and electronic components that must be handled responsibly to prevent environmental contamination.
When devices are discarded improperly, they can contribute to the growing problem of electronic waste. Hazardous substances present in electronic equipment may pollute soil and water if they are not recycled properly.
ITAD providers help organizations minimize their environmental impact by refurbishing reusable devices and recycling components in compliance with environmental standards. Functional devices can often be refurbished and reused, extending their lifecycle and reducing electronic waste.
By combining secure data destruction with responsible recycling practices, organizations can achieve both data security and sustainability objectives.
Creating a Secure IT Asset Disposal Policy
Every organization should establish a clear policy for managing end-of-life technology assets. A well-defined IT asset disposal policy ensures that employees understand the correct procedures for retiring and disposing of hardware.
The policy should include guidelines for asset tracking, approval processes for equipment disposal, and secure methods for data destruction. It should also define the roles and responsibilities of IT teams, security departments, and external service providers involved in the disposal process.
Asset inventories must be maintained to track devices throughout their lifecycle. When devices are retired, they should be securely stored until they are processed through approved ITAD procedures.
Regular audits can help ensure that the organization’s disposal policy is being followed and that no devices are being discarded without proper data sanitization.
The Role of Professional ITAD Providers
Managing IT asset disposal internally can be challenging for many organizations. Secure data destruction requires specialized tools, expertise, and compliance knowledge. This is why many companies partner with professional ITAD providers.
Experienced providers have the infrastructure required to handle large volumes of retired IT equipment while ensuring secure data destruction and environmentally responsible recycling. They follow strict procedures that comply with industry standards and regulatory requirements.
Professional ITAD services also provide detailed documentation of the disposal process. This documentation helps organizations demonstrate compliance during internal audits or regulatory inspections.
By outsourcing the process to experts, businesses can ensure that their data security remains intact while reducing the operational burden on internal IT teams.
Greentek Reman: Supporting Secure and Responsible IT Asset Disposition
When organizations look for reliable partners to manage their IT asset disposition processes, experience, transparency, and compliance expertise are critical factors. Greentek Reman has built a strong reputation as a trusted provider of sustainable IT lifecycle management and electronic waste recycling services.
The company specializes in responsible IT asset disposal solutions that prioritize both environmental sustainability and data security. By following structured ITAD processes, Greentek Reman ensures that retired IT equipment is handled safely from collection to final processing.